Our Cybersecurity Foundation Is Crumbling? | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium

🌸Crypto Eri 🪝Carpe Diem on Twitter: "Secret Sharing with Constant Communication Approved today. Posted IACR Privacy Protocol Research, sponsored in part by a grant/gift from @Ripple Labs. (This org is an initiative
![PDF) Low-Cost Solutions for Preventing Simple Side-Channel Analysis: Side-Channel Atomicity [Cryptology ePrint Archive, Report 2003/237] Benot Chevallier-Mames | Benoît Chevallier-Mames and Mathieu Ciet - Academia.edu PDF) Low-Cost Solutions for Preventing Simple Side-Channel Analysis: Side-Channel Atomicity [Cryptology ePrint Archive, Report 2003/237] Benot Chevallier-Mames | Benoît Chevallier-Mames and Mathieu Ciet - Academia.edu](https://0.academia-photos.com/attachment_thumbnails/47583629/mini_magick20190206-23501-3h6daj.png?1549472108)
PDF) Low-Cost Solutions for Preventing Simple Side-Channel Analysis: Side-Channel Atomicity [Cryptology ePrint Archive, Report 2003/237] Benot Chevallier-Mames | Benoît Chevallier-Mames and Mathieu Ciet - Academia.edu
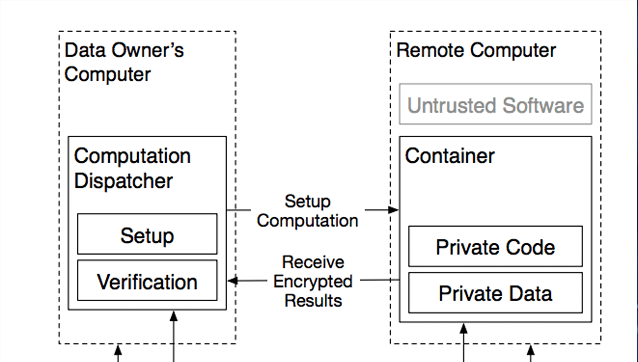
![PDF] State-free End-to-End Encrypted Storage and Chat Systems based on Searchable Encryption | Semantic Scholar PDF] State-free End-to-End Encrypted Storage and Chat Systems based on Searchable Encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/6c8f04d8134f85764d27bb546bc80b4cd0bdf9f4/7-Figure3-1.png)
PDF] State-free End-to-End Encrypted Storage and Chat Systems based on Searchable Encryption | Semantic Scholar








![How To] Check if Cryptology paper is published How To] Check if Cryptology paper is published](https://lh3.googleusercontent.com/-Y7TgfKU2LoM/YKaGEWPm4SI/AAAAAAABi50/XeY3ND7S0vcAkLaHfyxZ_DKyanKo2b0JwCLcBGAsYHQ/s16000/image.png)